This is the backbone of every business, but often the area where businesses try to cut costs.
For tech42, this process is second nature and something we take pride in. We get that no network is perfect, but for the past 10 years, tech42 managed networks have a 99.97% uptime. Most businesses don’t realize that a network needs 24/7 attention and services working behind the scenes to keep a healthy, functioning environment. With the help of tech42, we can work with your decision-making team to create an environment in which technology is always working at its best for your employees – keeping employee morale, productivity and customer support at an all-time high.
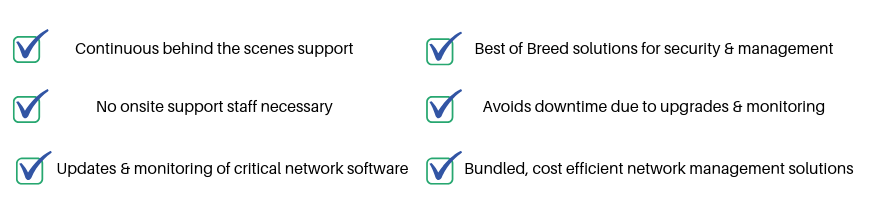
YOUR BENEFITS: